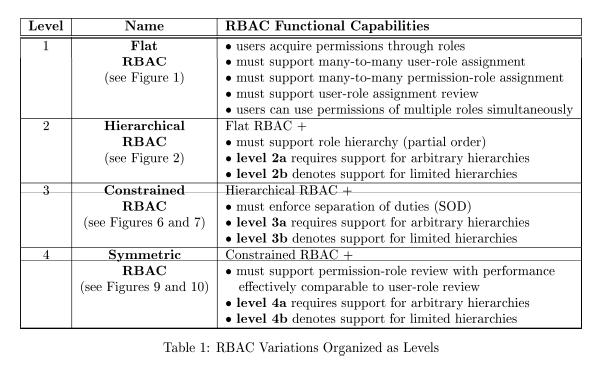
Table 1 from Evolution of access control models for protection of patient details: a survey | Semantic Scholar

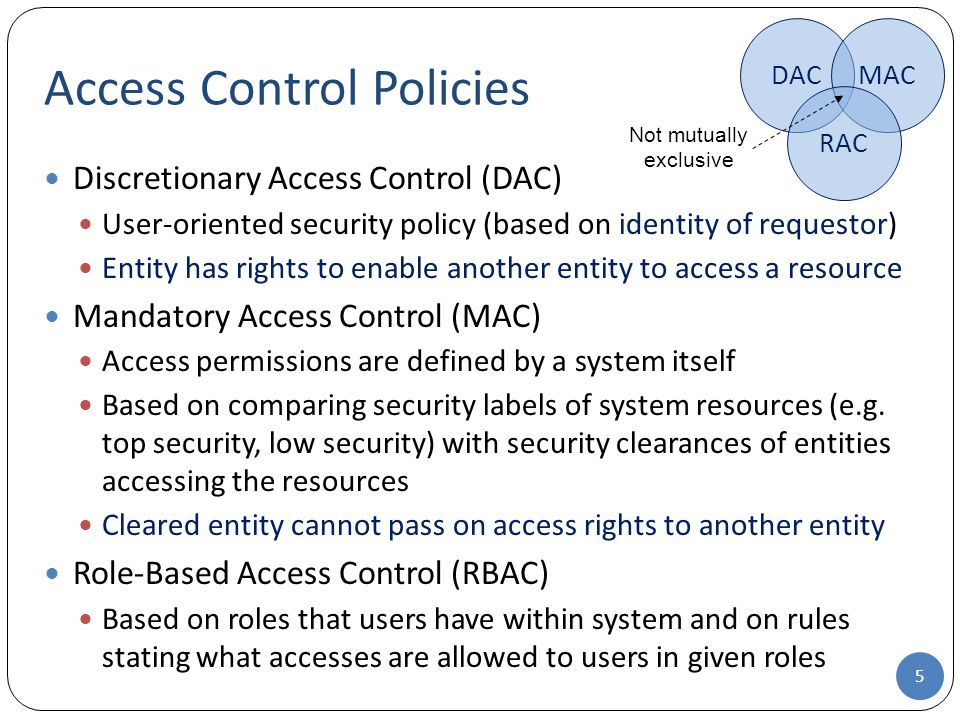
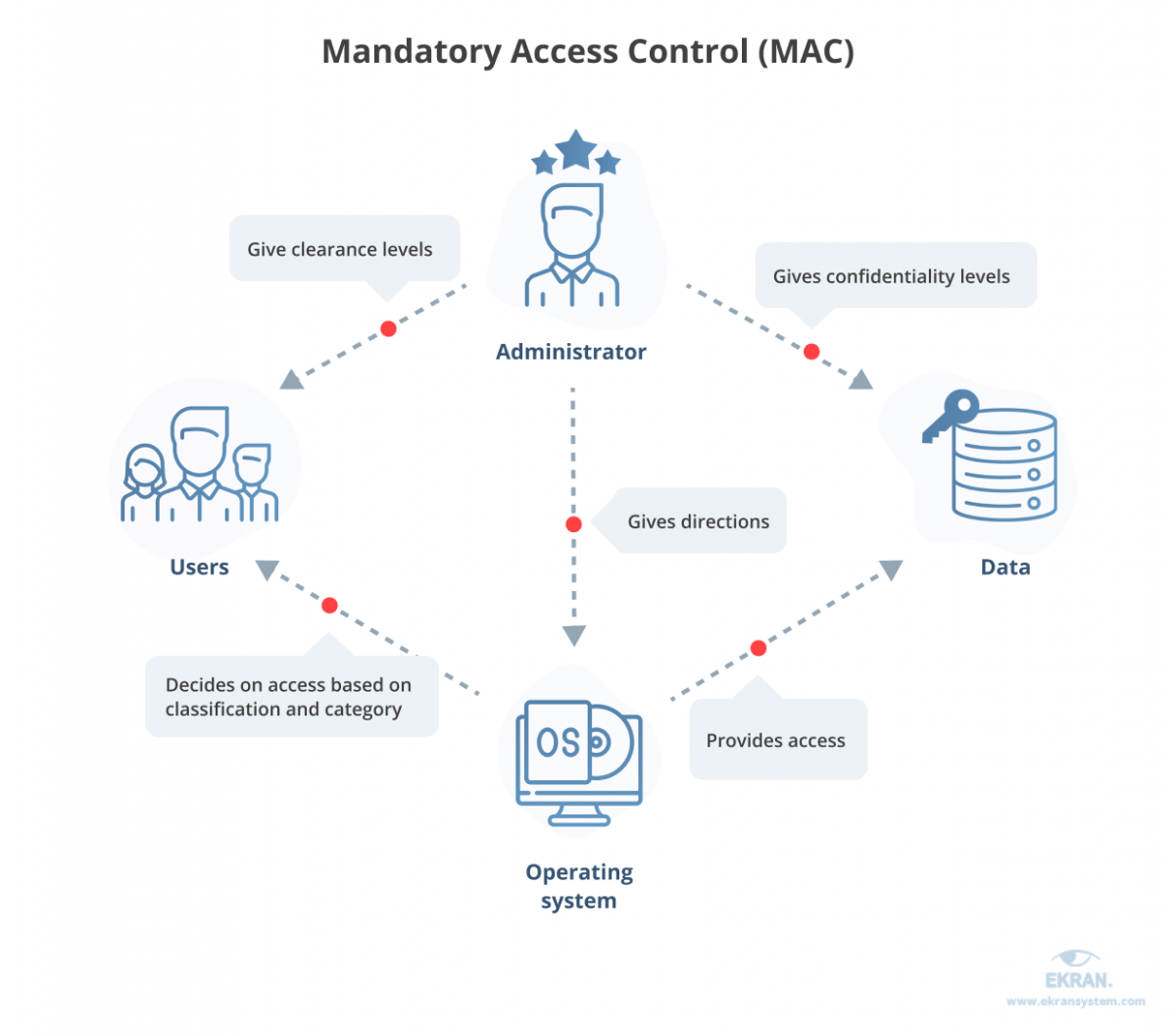
Difference between Discretionary Access Control(DAC) And Mandatory Access Control(MAC) l MAC Vs DAC - YouTube

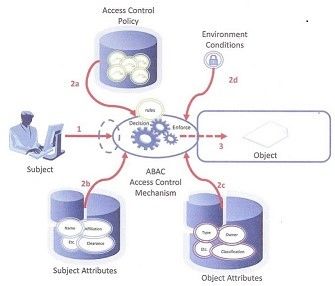
Towards Attribute‐Centric Access Control: an ABAC versus RBAC argument - Fatima - 2016 - Security and Communication Networks - Wiley Online Library



.png)

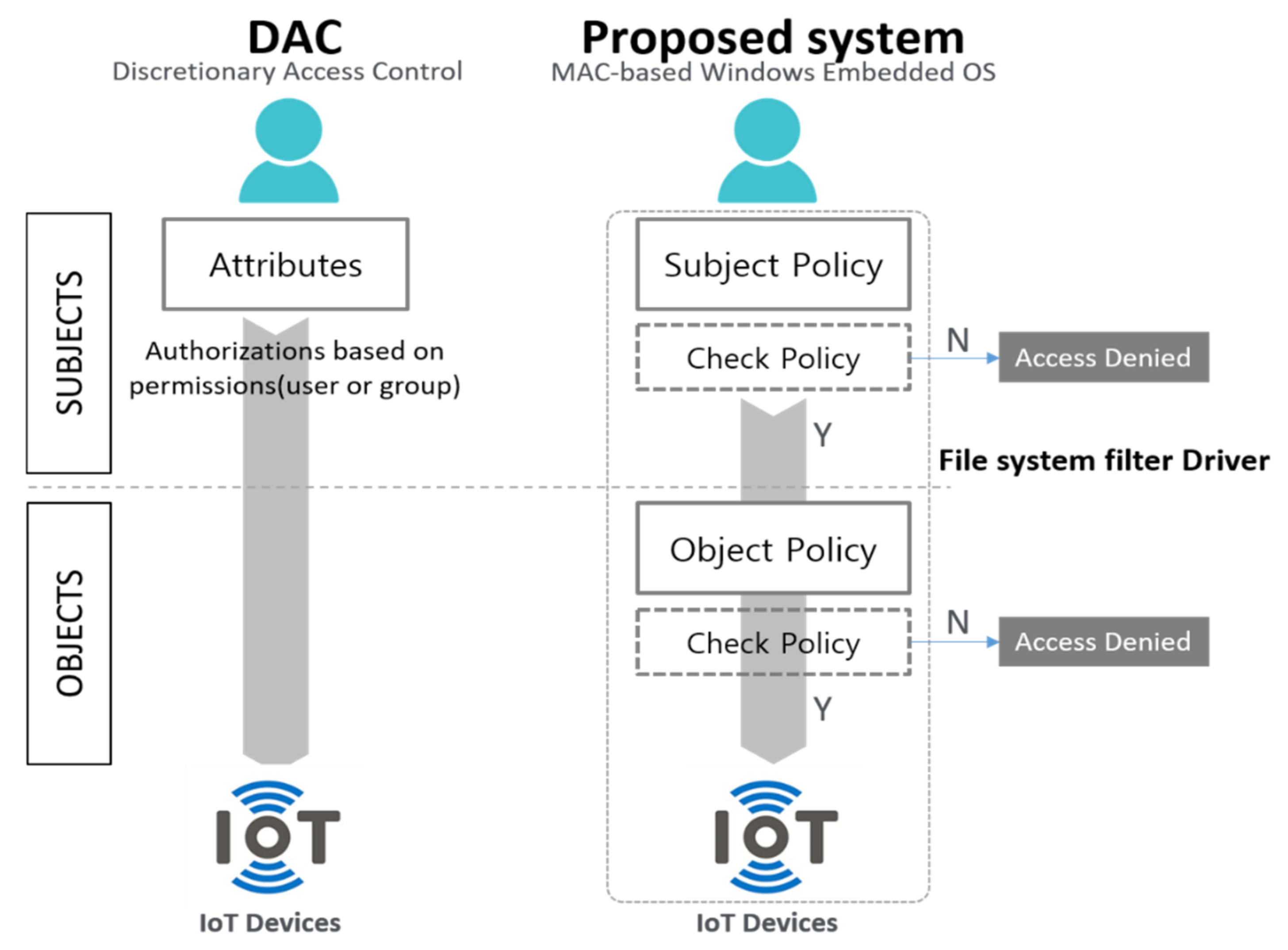





![PDF] A Configurable Framework for RBAC, MAC, and DAC for Mobile Applications | Semantic Scholar PDF] A Configurable Framework for RBAC, MAC, and DAC for Mobile Applications | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/98cf05e62c4957b9d1e0efc3c36dfd14abdd3b6d/33-Figure1.3-1.png)